Search engine optimization (SEO) is a long game. Improving your website to rank higher on search engine results pages can help you attract more traffic. In addition, it helps to build a reliable reputation. But some people like to create shortcuts using what is known as black hat SEO. If this happens, your company can pay the price.
What Is Black Hat SEO?
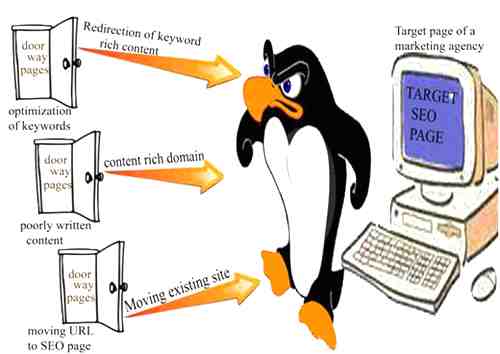
Black hat SEO is any activity that seeks to improve a website’s ranking and reputation by using methods that violate the terms of service of search engines such as Google or Bing.
In the early days of the internet, many marketers used black hat SEO tactics to increase their visibility, attract traffic, and build trust. But as search engines evolved and tried to improve the quality of search results, they imposed sanctions on unethical practices.
Now threat actors have embraced this old-fashioned subterfuge to exploit and steal well-established companies from unsuspecting online shoppers.
Why Do People Use Black Hat SEO?
Honest SEO (aka white hat SEO) takes a long time to pay off. Once your site ranks highly for competitive keywords, you seem like a trustworthy brand that potential customers will trust. Threat attackers have realized that the best way to rank a site quickly is to hijack a website with an already established reputation.
Attackers can clone your website — also known as domain spoofing — and then use black hat SEO tactics to drive traffic to their duplicate site. Someone can fake a website to sell low quality products to take advantage of the reputation of a trusted store. They can also use the forged domain as part of a phishing scam. Since the fake site looks almost identical to the bona fide brands, the scammers can fool customers by sharing their credit card details.
Once thieves have your personally identifiable information, they can make fake purchases and sell your information on the dark web.
The good news is that modern analytics and antivirus solutions can help detect phishing sites quickly. However, black hat SEO attackers can boost the rank of a fake domain and lure unsuspecting victims before the fake site is detected and shut down.
How Does Domain Spoofing Impact Your Business?
In the age of social proof, consumer trust is paramount. Your online reputation can make or break your business. When people use black hat SEO to copy your website, there are serious consequences.
You lose traffic. Since spoof websites mislead potential customers, your site will get fewer visitors. You miss out on sales and see a lower return on your marketing spend.
Consumers lose trust in your brand. Black hat SEO leads people to a fake website. They can then find poorly spun content, spam links, fake comments, and fraudulent ads. This poor user experience can make people look at your brand in a different light.
People leave bad reviews. This negative feedback may be aimed at a scam site, but the victims will blame you if it was under your brand name. The bad press can put off other customers.
Search engines can penalize your business. Sometimes a real company will suffer the consequences if their site does not meet the standards of search engines. A Google penalty can ban a site from search results. Traffic will drop and it may take a long time to recover.
Reduce the Chances of Customers Visiting a Cloned Website
If clients fall prey to financial fraud or identity theft and think it was your business, you could have a public relations nightmare.
It is best to stay ahead of this threat. Here are seven steps to help you prevent black hat SEO from misleading your customers to a counterfeit website:
Install a TLS Certificate
A Transport Layer Security (TLS) certificate is a digital security protocol that verifies the identity of a website and establishes an encrypted connection between the website and the user’s browser. Users can see the padlock and HTTPS prefix in your domain URL, giving them confidence that you keep their personal information private and secure.
Secure Your Source Code
Ideally, your developer should take security measures to protect your website from potential attacks. One such tactic is to disable the copy-paste feature on your site so that attackers cannot easily copy your source code.
Remain Proactive
Businesses must have vigilant security teams that proactively monitor their domain and traffic for suspicious behavior. When you have processes and strategies in place for data handling and risk management, you can improve the way you identify and defend threats.
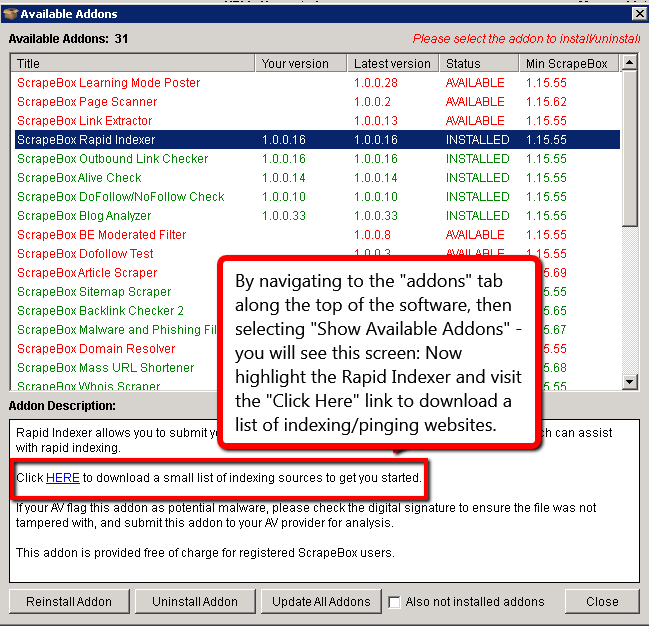
Use the rel=canonical Tag
A common aspect of website spoofing is to create duplicate pages of a real site and then make subtle changes to the URL, such as changing one letter. Adding the rel=canonical tag tells search engines that a specific URL is the master copy of a site page, making it more difficult for fraudsters to duplicate your site.
Study Your Website Analytics
Very often, scammers play for a quick win and may not take the time to change all the internal links. Even if visitors land on a cloned site, they can click on links to go to the legitimate, original domain. Check your website analysis to identify incoming traffic from a cloned site with a similar domain name.
You can also increase your chances of finding a duplicate site if you build a lot of internal links on your website. Fortunately, that’s also a good SEO practice to improve your site’s performance.
Take Action
Once you identify a fake site, act quickly to remove it. First enter the IP address. Contact your hosting provider and ask them to block all requests to the fraudulent site’s IP address.
Then send the provider or content delivery network a removal request. Provide clear details about the attack and any threats to your business or customers.
It also helps to copyright your brand. You can share copyrights and trademarks to speed up the removal process and add an extra layer of protection to your website.
Hire a Certified Ethical Hacker
It’s much harder for someone to harm your business with black hat SEO if they can’t also duplicate your domain or violate your website. By hiring a certified ethical hacker, you can find security gaps and vulnerabilities and stay one step ahead.
Restoring Your Reputation After a Spoof

The above tips will help you stop scammers. But by the time you take those actions, the impact of black hat SEO and a fake website may already have done some damage. In the worst cases, criminals sold counterfeit products, stole credit card information and carried out identity theft on consumers – all under your brand name.
What can you do to get people to trust you again?
Address the Situation Publicly
Don’t try to hide the problem. Create content that speaks directly to your customers, tell them you are aware of the situation and are working hard to repair the damage.
You could make a video for YouTube or Instagram where you publicly apologize to everyone affected. Even if it wasn’t your fault, it’s good to take some responsibility and accept that your security team can do more to protect your customers.
Remove Fake Reviews
People who use Black Hat SEO often add fake online reviews to increase the credibility of their fake website. Contact search engines and third-party review platforms such as Trustpilot and ask them to remove fake reviews.
Add Multi-Factor Authentication
Ecommerce stores should always have these security measures in place to protect customers. It is worth pointing out that cyber criminals can exploit the CAPTCHA system. Fraudsters will add these tests to fake domains to trick visitors into thinking they are on a legitimate, safe site.
Communicate Openly About Your Policies
Share your policies for communication with your customers. For example, if you use two-step verification, make that clear so people know to expect it. If they don’t get a two-factor authentication request on their phone or email, they may know they’re not on a real site.
Site spoofing can confuse customers and steal money from both them and their businesses. It is part of current good online hygiene to keep an eye on black hat SEO.
With a passion for creative writing and an unquenchable thirst to learn about futuristic technology, Christopher John Haughey made the transition from journalism to…